2026/03/20
2026 Digital Resilience: The Complete Guide to System Maintenance and Project Takeover-Ending the "Software Orphan" Crisis
In a rapidly evolving digital era, System Maintenance and Project Takeover are the lifelines for business continuity. Many enterprises face the dilemma of original vendors closing down, technical team turnovers, or legacy systems with poor performance and no support. If left unaddressed, this "Technical Debt" becomes the biggest hidden risk to business expansion.
TWJOIN possesses extensive experience in technical takeovers and a rigorous maintenance framework. We don’t just fix bugs; through professional Code Reviews and Architectural Restructuring, we help enterprises regain control over their digital assets, ensuring your web systems and applications continue to create value in a secure and stable environment.
👉 Free Consultation / Feasibility Assessment- Digital Asset Defense: Why Enterprises Need Professional System Takeover Services in 2026?
- Pre-Takeover Assessment: Evaluating the Maintenance Value of Your System
- Unveiling Maintenance Costs: Why "Preventive Maintenance" is Cheaper than "Disaster Recovery"
- The 5-Step Professional Takeover: From Code Scanning to Production Handover
- Technical Debt Management: Optimization Strategies for Legacy Systems
- Regaining Digital Sovereignty: Legal Practices for Source Code Integrity and Hosting Access
- 2026 Recommended List: Professional System Maintenance & Project Takeover
- TWJOIN: Breathing New Life Into Your Legacy Systems
- Deep Q&A: 10 Core Pain Points of Enterprise System Maintenance
- Conclusion: Choosing the Right Maintenance Partner—Turning Technical Debt into Digital Assets
Digital Asset Defense: Why Enterprises Need Professional System Takeover Services in 2026?
In the face of increasingly complex web technologies and cyber threats, system maintenance is no longer just about "keeping the lights on." The value of a professional takeover lies in:
- Bridging Technical Gaps : Resolving functional stagnation caused by lost contact with original developers, ensuring the continuity of business logic.
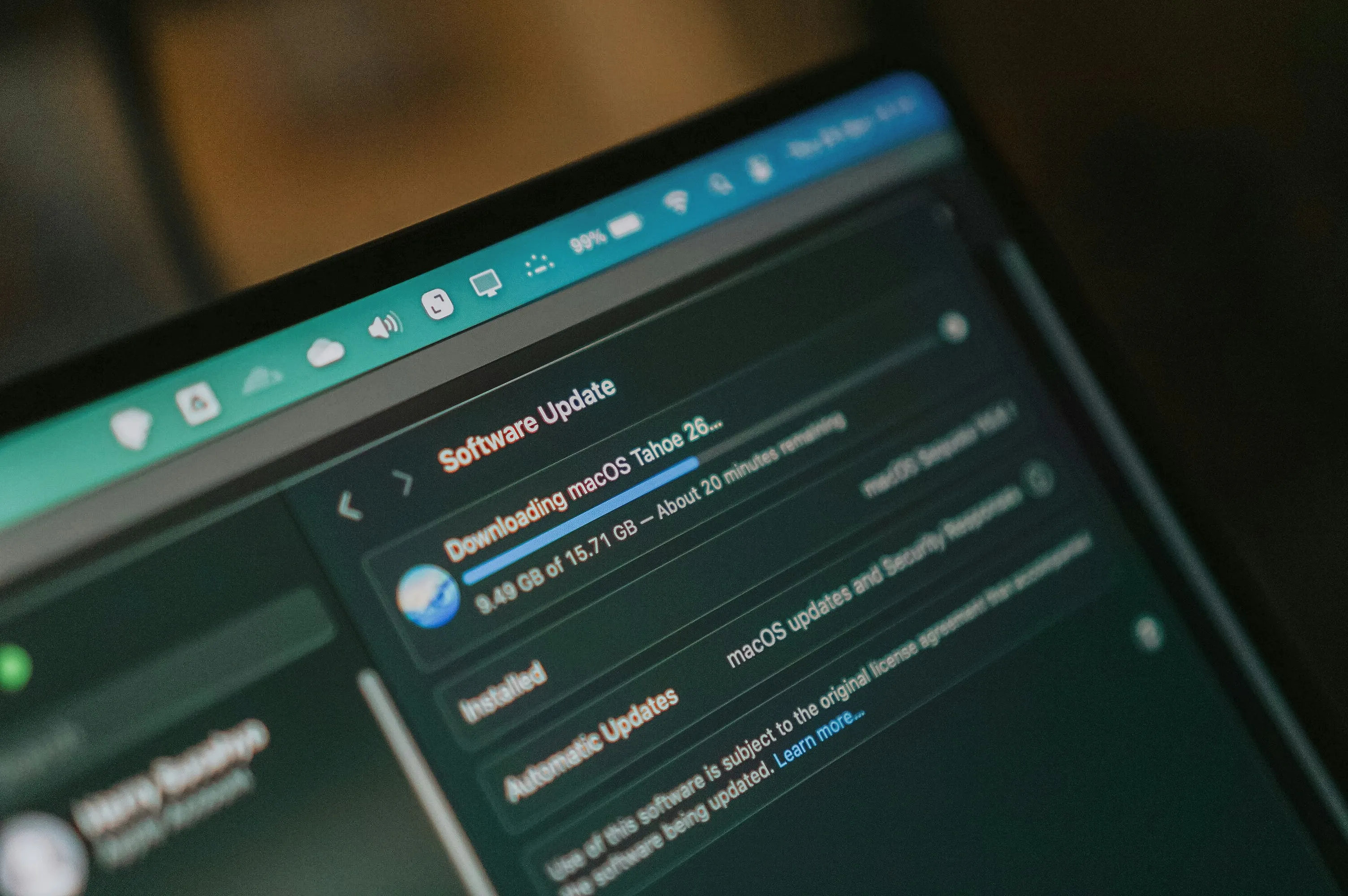
- Vulnerability Patching : Implementing security updates for outdated frameworks or libraries (such as legacy Node.js or PHP versions) to prevent hackers from exploiting Zero-day vulnerabilities.
- Performance Breakthroughs : Enhancing the loading speed of legacy sites through database indexing optimization and caching mechanism restructuring, thereby improving Google SEO rankings.
- Compliance Maintenance : Ensuring systems meet the latest 2026 data privacy regulations (GDPR/CCPA) to avoid legal risks arising from improper project handovers.
Pre-Takeover Assessment: Evaluating the Maintenance Value of Your System
Not every system is worth saving. A professional technical team evaluates the following dimensions, which are also key indicators in determining "Takeover Fees":
- Code Quality : Is the code readable with basic documentation or comments? Or is it overwhelmed by "Spaghetti Code"?
- Framework Universality : Does it use mainstream technologies (e.g., Node.js, PHP Laravel, React)? Using obscure or deprecated languages will cause maintenance costs to grow exponentially.
- Source Code Integrity : Does it include original frontend code (Vue/React), backend logic, and database migration files?
- Hosting Control : Do you have Root or Administrator access to cloud platforms (AWS/GCP/Azure)?
- Third-Party Dependency : How many external APIs (Payment, Logistics, Maps) are integrated? Are these service links still active and valid?
Unveiling Maintenance Costs: Why "Preventive Maintenance" is Cheaper than "Disaster Recovery"
Many business owners are accustomed to the "fix it when it breaks" mentality. However, in 2026, this approach can lead to staggering losses:
- Downtime Cost : For an e-commerce platform, a single hour of downtime means more than just lost immediate orders; it often drives customers straight to your competitors.
- Data Breach Risks : Without regular Security Patch updates, the cost of legal compensation and brand repair following a security incident far exceeds routine maintenance fees.
- Technical Debt Interest : Unstable code exponentially increases the difficulty of developing new features. What should have been a one-week task can easily turn into a month of work.
- TWJOIN Advocates "Proactive Maintenance" : We provide fixed maintenance services based on system complexity, including regular backups, environment updates, performance monitoring, and emergency response within one hour.
The 5-Step Professional Takeover: From Code Scanning to Production Handover
A successful project takeover must follow a rigorous process to prevent system crashes during the transition:
- Permission & Asset Inventory : Reclaim full ownership and access to all servers, domains, SSL certificates, third-party APIs, and external databases.
- Code Audit : Conduct security scans using automated tools to identify high-risk vulnerabilities such as SQL Injection or XSS .
- Local & Staging Environment Reconstruction : Attempt to recompile and run the system on developer machines and cloud staging environments to ensure the provided source code is "live" and functional.
- Logic Mapping & Documentation : Perform reverse engineering and documentation for obscure business logic, such as complex profit-sharing algorithms or discount engines.
- Production Switch & Monitoring Activation : Execute the environment switch during off-peak hours and simultaneously activate 24/7 Uptime and resource consumption monitoring.
Technical Debt Management: Optimization Strategies for Legacy Systems
After taking over, we typically adopt one of three strategies based on the system’s condition:
- Maintenance (Keep Alive) : For systems nearing retirement, we focus solely on security patches and basic operational stability to minimize expenditures.
- Refactoring : For core business systems, we optimize the underlying code architecture and database performance without altering existing functionalities.
- Incremental Modernization (Strangler Pattern) : Gradually decomposing legacy functions into new microservices or modern APIs to ensure a smooth and seamless transition.
Regaining Digital Sovereignty: Legal Practices for Source Code Integrity and Hosting Access
In the process of a system takeover, legal compliance and asset handover are just as critical as the technical transition:
- Source Code Verification Standards : Confirming that the provided code is compilable and functional, and ensuring it contains no malicious backdoors.
- Third-Party Account Transfer : Executing the transfer of ownership and administrative rights for domain registrars, SMS gateways, payment platforms, and more.
- Intellectual Property (IP) Declaration : Clearly defining the final ownership of development results and source code within the contract to protect the enterprise's digital sovereignty.
2026 Recommended List: Professional System Maintenance & Project Takeover
| Company Name | Service Core | Market Reputation & Technical Features |
|---|---|---|
| ACubeDT | Cloud Maintenance | Specialized in cloud environment load balancing and performance tuning. |
| TWJOIN | System Takeover, Code Audit, Long-term Maintenance | Expert in complex business logic takeovers and automated DevOps. Emphasizes 100% source code delivery and IP transparency. Strong documentation recovery with extensive cross-border project experience. |
| Sunlight | Industrial Transformation | Providing stable subsequent technical support for enterprise digital transitions. |
| Fable | Tech Consulting, Product Validation | Evaluating the feasibility of pivoting legacy systems to new business models; ideal for early-stage startups. |
| NSS | Web Hosting, Security Monitoring | Offering standardized hosting and web maintenance; ideal for clients prioritizing infrastructure stability. |
TWJOIN: Breathing New Life Into Your Legacy Systems
In the realm of system maintenance, technical prowess is essential, but "understanding business logic" and "standardized processes" are the true keys to success. TWJOIN helps enterprises transform technical debt into operational assets.
In-depth Code Audit
We never take over blindly. Our senior architects conduct a thorough "health check" on your codebase at the initial stage, identifying deprecated libraries, logic backdoors, and optimizing database queries.
IP Transparency & Knowledge Transfer
TWJOIN guarantees 100% source code delivery for every optimization performed after the takeover. We don't believe in "vendor lock-in" through copyright; we build trust through high-quality service.
Proactive Defensive Maintenance
Maintenance is more than just fixing bugs. With real-time monitoring and preventive updates, we ensure your system stands resilient against the latest cybersecurity threats.
Deep Q&A: 10 Core Pain Points of Enterprise System Maintenance
Q1: Our original developer is unreachable. Can you take over our project directly?
A: Certainly. As long as you possess the project specifications and source code, we can proceed with the takeover and continued development.
Q2: What does your system maintenance service include?
A: Our services cover regular backups, system environment updates, security vulnerability patching, database optimization, and essential bug fixes.
Q3: Why is there a "Takeover Fee" for existing projects?
A: This fee covers the labor costs for environment restoration, permission auditing, code scanning, and setting up a dedicated staging environment.
Q4: Will you rewrite the entire original codebase after taking over?
A: Unless there are severe security threats, we prioritize "stable continuity" and perform optimizations incrementally.
Q5: How do you ensure the project doesn't crash during the transition?
A: We simulate the entire takeover process in a staging environment first. We only switch to production after verifying everything is error-free to minimize risk.
Q6: Can you maintain our system if we don’t have the source code?
A: That is extremely difficult. Without source code, we typically recommend partial refactoring or rebuilding the system.
Q7: Is a yearly contract required for system maintenance?
A: We recommend annual or semi-annual contracts to ensure a stable allocation of technical staff for consistent monitoring.
Q8: Can you help resolve high cloud hosting bills (AWS/GCP)?
A: Yes. We provide architectural optimization recommendations to reduce redundant resource consumption and lower costs.
Q9: What is a "Code Audit," and what are its benefits?
A: It identifies hidden bugs and security backdoors, ensuring your system isn't a "time bomb" waiting to go off.
Q10: What are the risks of low-cost maintenance services?
A: Common issues include lack of regular backups, stagnant technical updates, and an inability to provide immediate response during security incidents.
Conclusion: Choosing the Right Maintenance Partner—Turning Technical Debt into Digital Assets
System maintenance and project takeover are tests of a team's accountability and standardized processes. A stable system is the most solid foundation for enterprise growth. If you are struggling with system instability, TWJOIN is ready to help you resolve the technical chaos and restore order.
🚀 Ready to safeguard your digital assets with TWJOIN?
👉 Learn about our Maintenance & Refactoring👉 Or contact us directly